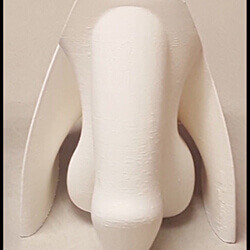
Months After Hackers Demand Ransom to Unlock Chastity Cages, QIUI Plans Release of Cellmate 2
Consumers raise alarm as rumored electric shock feature added, but no mention of security improvements.

Despite having their Bluetooth chastity cages hacked last year, QIUI reportedly plans to release the Cellmate 2 Chastity Cage. Upgrades are rumored to include a removable wireless charging base, a new version of the app, automatic unlocking, and… electric shock functionality.
How hackers took control
The Chinese sex toy manufacturer made headlines in October 2020 after reports came in that their app-controlled Cellmate Chastity Cages were remotely locked by hackers. These hackers sent ominous messages claiming “Your c*ck is mine now” and demanded $750 worth of Bitcoin in exchange for unlocking the device.
QIUI issued an apology shortly after and released a new version of the app addressing the vulnerabilities—but the company has not acknowledged security concerns since then.
A shocking new version
Now rumors are circulating that QIUI will be releasing a second version of their notorious chastity cage.
Kyle Machulis, the engineer behind buttplug.io, was the first to publicly speak about this news on the Buttplug Twitter page.
He described QIUI as a “company that should never be allowed to produce hardware again, much less BDSM hardware” and later added “Do not bother showing up in my mentions with ‘But what if they make it safe?’ That is not a thing that can happen.”
Machulis’ thread includes a screenshot giving merit to the rumors that these new cages will include electrostimulation. He received the screenshot from someone in his community living in China and believes they are from either a Chinese QIUI blog or social media feed.
QIUI hasn’t commented on exactly how this functionality will be implemented.
No mention of security improvements
Sex toy companies offering potentially dangerous devices are a concern for the entire industry. User security should be paramount—especially when it comes to BDSM products that lock or which include higher risk functionality like electric shock.
Earlier this year, malware collection vx-underground leaked the source code responsible for the Cellmate attack. The code shows how hackers abused QIUI’s API in order to enumerate user information, send messages to the victim’s app, and request ransoms, among other malicious acts.
Trying to target the same API endpoints today results in an error, but this doesn’t mean that another similar attack against the Cellmate device won’t be possible in the future.
It’s unclear whether QIUI is taking these concerns seriously. While they seem to have fixed the known vulnerabilities, no publicly available information about the Cellmate 2 mentions security improvements or steps they’ve taken to make their devices safer for users.
Image sources: QUIU